2024년 대한민국 베스트 라이브카지노 리뷰
디지털 시대가 꽃피우면서 온라인 카지노 산업은 지난 몇 년 동안 급속도로 성장해왔습니다. 특히 라이브카지노는 리얼 카지노의 현장감을 그대로 제공하면서도 집에서도 플레이 할 수 있어 한국 사용자들에게 큰 사랑을 받고 있습니다. 2024년 수많은 라이브 카지노 플랫폼 중 어떤 사이트가 한국인들에게 가장 인기 있고, 어떤 특별한 경험을 제공하는지 궁금하지 않으신 가요? 한국인들에게 가장 주목 받는 베스트 라이브 카지노 플랫폼들을 추천하고, 각 플랫폼의 특징과 장점을 소개해 드리겠습니다.
2024년 베스트 라이브카지노 리뷰
국인들에게 인기 있는 7가지 베스트 라이브 카지노 사이트를 상세히 살펴봅니다.
- 벳위즈(BetWiz) – 매일 캐시백을 제공하는 라이브카지노
- 조이카지노(Joycasino) – 다양한 변형 스타일을 제공하는 라이브카지노
- 본즈(Bons) – 전용 모바일 앱을 지원하는 라이브 카지노
- 아톰 카지노(Atom Casino) – 최고의 11개 게임 제작사들이 개발한 라이브카지노
- 슈퍼헐크(Superhulk) – 5% 페이백 보너스 제공의 라이브카지노 플랫폼
- 체스 카지노(Chess Casino) – 라이브 딜러 카지노와 슬롯 중심의 플랫폼
- 소닉 카지노(Sonic Casino) – 라이브카지노 첫 고객 30% 입금 보너스 제공
1. 벳위즈(BetWiz) – 매일 캐시백을 제공하는 라이브카지노

벳위즈 카지노는 사용자들에게 다양한 이벤트와 프로모션을 제공하고, 토너먼트를 통해 다른 참가자들과의 경쟁이 흥미진진하며, 벳위즈 특유의 원더 휠로 무료 스핀과 같은 보상을 얻을 수 있습니다. 이런 장점들은 신규 사용자 뿐만 아니라 기존 사용자들도 계속해서 이 플랫폼을 이용하게 만듭니다.
특히, 매일 제공되는 특별 보너스는 다른 카지노와 비교했을 때 내세울 수 있는 장점입니다. 처음 가입하는 사용자는 카지노 부분에서 20%의 웰컴 보너스와 매일 5%의 캐시백을 얻을 수 있고, 추가로 0.5%의 리베이트 보너스와 모든 게임에서 미적중 시 특별 보너스를 받게 됩니다.
온라인 라이브카지노에서는 에볼루션에서 제공하는 한국어 딜러와의 라이브 바카라를 체험할 수 있습니다. 플레이어는 카지노 딜러와 직접 대화하고 다른 국내 참가자들과도 소통하는 채팅 기능을 이용할 수 있습니다. 게임 인터페이스에서는 최소 배팅 금액과 사이드 배팅 선택 등의 옵션을 살펴볼 수 있습니다.
- 보너스: 20%의 웰컴 매칭 보너스, 0.5%의 리베이트 보너스, 미적중 보너스, 매일 순손실에 대한 5% 캐시백
- 지원 게임: 라이브카지노, 스포츠 베팅, 바카라, 블랙잭, 룰렛, 슬롯 등
- 주요 특징: 한국어 고객 지원, 유명 게임 개발사의 라이브카지노 사이트
2. 조이카지노(Joycasino) – 다양한 변형 스타일을 제공하는 라이브카지노
2014년부터 운 영 중인 라이브카지노 플랫폼 조이카지노는 전세계적으로 평판이 좋은 게임 개발사들과 협업하여 프리미엄 퀄리티의 게임을 제공하고 있습니다. 전통적인 랜드 카지노에서 즐길 수 있었던 딜러와 함께하는 게임을 집에서 편안하게 체험할 수 있고, 기존 카지노에서는 경험하기 힘들었던 새로운 스타일의 게임쇼도 선보입니다.
대표적으로 라이트닝 룰렛, 인피티니 블랙잭, 빠른 바카라, 스퀴즈 바카라, 풋볼 스튜디오, 드래곤 타이거, 슈퍼 식보 등이 있으며, 이 게임들은 다른 곳에서 경험하기 어려운 독특한 게임들로 잘 알려져 있습니다.
조이카지노는 4,000개를 넘는 다양한 게임 라이브러리를 자랑합니다. 게임 종류는 라이브카지노부터 슬롯, 스포츠 베팅까지 다양합니다. 신규 회원을 위한 200% 매칭 보너스와 무료 스핀을 제공하여 게임의 다양성을 체험할 수 있게 돕고 있습니다. 풍부한 게임 컨텐츠로 모든 한국 플레이어의 취향에 맞는 게임을 찾을 수 있을 것이라 확신합니다.
- 보너스: 200%의 웰컴 매칭 보너스, 0.25%의 리베이트 보너스 등
- 지원 게임: 라이브카지노, 스포츠 베팅, 블랙잭, 룰렛, 슬롯 등
- 주요 특징: 방대한 게임 라이브러리, 최대 200% 첫 입금 보너스
3. 본즈(Bons) – 전용 모바일 앱을 지원하는 라이브카지노

본즈 카지노는 슬롯, 룰렛, 그리고 다양한 테이블 게임을 제공하는 온라인 카지노 플랫폼입니다. 암호화폐 지원이 특징인 이 플랫폼에서는 비트코인과 이더리움을 비롯한 총 7가지 암호화폐로 거래를 할 수 있고, 모든 거래는 즉시 처리되어 게임 참여가 빠릅니다.
본즈 카지노는 모바일 환경 최적화를 위한 자체 앱 또한 선보여 많은 사용자들로부터 최상의 모바일 카지노 중 하나로 인정받고 있습니다. 입금 금액에 따라 다양한 보너스 제공이 특징적입니다. 일반적으로 200% 보너스가 제공되며, 최대 50달러까지 받을 수 있습니다. 그러나 500달러 이상을 입금하면 100%의 매칭 보너스를 받을 수 있고 이는 최대 2000달러까지 확장됩니다. 각각의 보너스에는 다른 웨이저링 요구사항이 부여되고, 모든 보너스에는 추가로 200개의 무료 스핀이 포함됩니다.
본즈 카지노는 또한 다양한 스포츠 이벤트에 베팅할 수 있는 스포츠 베팅 서비스도 제공하고 있습니다. 이 중에는 30여 가지 이상의 스포츠 종목과 e스포츠 베팅까지 포함되어 있습니다. e스포츠에는 우리가 잘 알고 있는 리그 오브 레전드와 도타2와 같은 게임들이 준비되어 있습니다.
- 보너스: 일반 보너스는 200%를 최대 $50까지 제공, 무료 스핀 200개가 모든 웰컴 보너스로 제공
- 지원 게임: 라이브 카지노, 스포츠 베팅, 바카라, 블랙잭, 룰렛 등
- 주요 특징: 다양한 형태의 웰컴 보너스, 암호화폐 7개 지원, 저렴한 최소 예치금
4. 아톰 카지노(Atom Casino)– 최고의 11개 게임 제작사들이 개발한 라이브 카지노
아톰카지노는 다양한 카지노 게임, 슬롯, 그리고 특별한 미니게임들을 제공하는 온라인 플랫폼입니다. 이 미니게임들은 특히 높은 수익률로 주목받고 있습니다. 카지노 게임은 에볼루션, 드림 카지노, 벳게임즈, 스카이윈드 등 11개의 게임 제작 스튜디오에서 제공되는 다양한 타이틀로 구성되어 있습니다.
슬롯 게임은 레드타이거, 노리밋 시티, 빅타임게이밍 등 총 22개의 게임 스튜디오가 제공하는 게임들로 이루어져 있습니다. 아톰카지노는 국내에서 높은 콤프 지급률로도 알려져 있습니다. 신규 가입자들은 30%의 웰컴보너스를 받을 수 있으며, 재충전 시에도 추가적인 보너스가 지급됩니다.
플레이어의 로열티 레벨에 따라 다양한 콤프가 제공되고, 카지노와 슬롯 각각에서 최대 1.1%와 4%까지의 콤프를 받을 수 있습니다. 다양한 보너스 이벤트와 함께 지인 추천 이벤트 등의 프로모션도 진행되고 있습니다.
- 보너스: 30%의 첫 입금 매칭 웰컴 보너스, 매 충전 시 15%의 추가 보너스 지급 등
- 지원 게임: 라이브 카지노, 스포츠 베팅, 슬롯 머신, 테이블 게임, 비디오 포커 등
- 주요 특징: 경쟁적인 배당 미니게임, 한화로 계좌이체 가능, 최대 1.1% 카지노 콤프
5. 슈퍼헐크 카지노(Superhulk) – 5% 페이백 보너스 제공의 라이브 카지노 플랫폼

슈퍼헐크 카지노는 온라인 게임과 스포츠 배팅을 제공하는 종합 플랫폼입니다. 첫 충전 시 30%의 보너스와 매 충전마다 15%의 혜택을 제공하는 것이 특징입니다. 이 서비스는 스포츠 배팅을 시작으로 확장하여 슬롯 게임과 라이브 딜러 카지노 게임을 추가하였습니다.
슈퍼헐크에서는 매일 150개 이상의 다양한 스포츠 이벤트가 진행되고, 축구부터 e스포츠까지 다양한 베팅 옵션을 제공합니다. 라이브 중계는 슈퍼헐크 TV를 통해 진행되어 실시간으로 게임을 관람하며 배팅을 할 수 있습니다. 웹사이트는 사용자 친화적으로 설계되어 있어 배팅 카트를 통해 쉽게 배팅을 관리하고 파워볼, 파워사다리 등의 미니 게임을 즐길 수 있습니다.
카지노 게임에서는 에볼루션 게이밍과 프라그마틱 프레이의 라이브 딜러 게임을 제공하고 있으며, 스피드 바카라나 스피드 블랙잭 등이 인기를 끌고 있습니다. 슬롯 게임 부문에서는 마이크로게이밍, 하바네로, 플레이앤고의 게임을 제공하고 있어 다양한 게임을 즐길 수 있습니다.
- 보너스: 첫 충전 시 30%의 보너스, 매 충전 시 15% 보너스 혜택 등
- 지원 게임: 라이브 카지노, 스포츠 베팅, 아시아 게이밍, 프라그마틱 플레이, 드림 게이밍 등
- 주요 특징: 100%, 30% 충전 보너스, 1.1% 카지노 콤프, 돌발 이벤트
6. 체스 카지노(Chess Casino) – 한국 플레이어에게 인기 있는 라이브 딜러 카지노와 슬롯 중심의 플랫폼

이 라이브 카지노 사이트는 다양한 이벤트와 프로모션을 제공하여 플레이어들을 끌어들이는데, 신규 가입자에게는 첫 충전 보너스와 매번 충전할 때마다 보너스를 제공합니다. 이뿐만이 아니에요! 지인 추천, 리뷰 작성, 간식 및 야식 이벤트, 출석 체크 이벤트, 연승 혹은 연패 보너스, 텔레그램 친구 추가 및 구독 이벤트 등 다양한 프로모션도 진행하고 있습니다. 이러한 혜택들로 인해 체스카지노는 많은 프로모션을 제공하는 카지노 플랫폼 중 하나로 한국인들에게 잘 알려져 있습니다.
게임 면에서도 체스카지노는 플레이어들에게 다양한 선택지를 제공합니다. 다양한 슬롯 프로바이더와 카지노 게임 프로바이더와의 협력을 통해 슬롯, 카지노 게임, 미니 게임 등을 제공하고 있습니다. 각 게임 카테고리에서는 콤프 이벤트를 통해 플레이어들에게 추가적인 혜택을 제공하고, 게임을 즐기는 동안 다양한 보너스를 즉시 받을 수 있습니다.
- 보너스: 30%의 첫 충전 보너스, 매 충전 시 15% 보너스, 1.1%의 카지노 콤프, 5% 페이백 보너스 등
- 지원 게임: 라이브카지노, 스포츠 베팅, 바카라, 크래쉬, 슬롯, 룰렛 등
- 주요 특징: 카지노 콤프 이벤트, 첫 충전 보너스, 24시간 고객 서비스
7. 소닉 카지노(Sonic Casino) – 라이브 카지노 첫 고객 30% 입금 보너스 제공

소닉카지노는 신규 회원들에게 풍부한 보너스 혜택을 제공하고 있는데, 롤링 콤프 상향 부스터, 카지노 입금 플러스, 슬롯 입금 플러스 보너스 등이 포함되어 있습니다. 첫 입금 시 특정 비율의 보너스를 지급하고, 한국 플레이어들을 위해 여러 국내 은행으로 충전이 가능합니다.
소닉카지노의 홈페이지는 사용 친화적으로 디자인되어 있으며, 주요 메뉴로는 라이브 카지노, 슬롯 게임, 미니 게임, 입금 신청, 출금 신청 등이 있습니다. 계정 생성 후, 사용자는 베팅 내역, 경기 결과, 이벤트, 공지사항, 마이페이지, 추천 내역 등 다양한 정보를 손쉽게 확인할 수 있습니다.
이 플랫폼은 고객 서비스에 중점을 두고 있습니다. 홈페이지 하단의 라이브 채팅을 통해 언제든지 문의할 수 있으며, 그 외에도 텔레그램과 카카오톡을 통한 문의 서비스도 제공하고 있어 한국 사용자가 편리하게 문의할 수 있는 다양한 방법을 제공하고 있습니다.
- 보너스: 첫 입금 시 30% 보너스, 콤프 상향 부스터, 카지노 입금 플러스, 슬롯 입금 플러스 보너스
- 지원 게임: 라이브카지노, 스포츠 베팅, 라이브 스포츠 게임, 미니 게임, 라이브 스코어 등
- 주요 특징: 30개 이상의 소프트웨어와 제휴, 사용 친화적인 웹사이트
기타 주목할 만한 라이브카지노 살펴보기
위 Top 7 라이브카지노 사이트 외에 추가로 6가지 주목할 만한 라이브카지노 사이트를 소개해 드립니다.
1. 메가 다이스(Mega Dice) – 200%의 입금 보너스와 무료 스핀 제공의 신규 라이브카지노
퀴라소의 공식 라이선스를 보유한 메가 다이스 는 실시간 라이브 카지노 경험을 제공합니다. 일반적인 비트코인 카지노와는 달리 KYC 문서 제출의 필요 없이 간편한 회원 가입 절차를 거칩니다.
메가 다이스는 신규 사용자들에게 특별한 입금 보너스를 제공합니다. 최소 $20 입금 시, 최대 1 BTC의 200% 보너스를 받을 수 있습니다. 이 보너스를 출금하려면 베팅 요구사항을 6배 초과로 완료할 때마다 10%의 보너스가 해제됩니다.
이 플랫폼에서는 대략 5,000개의 슬롯 게임을 즐길 수 있고, 80개가 넘는 게임 제작사들이 제공하는 500개 이상의 테이블 게임과 라이브 딜러 게임도 이용할 수 있습니다. 또한, 메가 다이스에서 제공하는 스포츠 베팅은 35가지 스포츠 게임을 제공하며, 축구, 배구, 테니스, 스키 등 다양한 종목에서 베팅을 즐길 수 있습니다. 메가 다이스는 비트코인을 비롯하여 이더리움, 테더, 도지코인, 라이트코인 등 여러 알트코인으로의 입출금 서비스를 제공합니다.
- 보너스: 최소 $20을 입금하면 최대 1BTC까지의 200% 매칭 입금 보너스
- 지원 게임: 라이브 스포츠, 가상 스포츠, 미니 게임, 카지노, 슬롯 등
- 주요 특징: 신규 가입자를 위한 특별 보너스, 약 5,000개의 슬롯 게임 제공 등
2. 토스카지노(Toss Casino) – 환전 대기 시간 없는 라이브 카지노
토스 카지노는 여러 라이브 카지노 제작사와 협력하여 플레이어들에게 실시간으로 딜러와의 게임을 제공하고 있습니다. 드림게임, 에볼루션, WM카지노와 같은 유명한 라이브 카지노 제작사들과의 협력을 통해 플레이어들은 흥미진진한 게임 경험을 얻을 수 있습니다. 또한, 비디오 슬롯 게임에는 프라그마틱 플레이, 에보플레이와 같은 선두 주자들의 게임도 즐길 수 있습니다.
토스 카지노는 첫 충전 시 특정 비율의 웰컴 보너스가 제공됩니다. 다양한 입금 보너스와 텔레그램 커뮤니티를 통한 돌발 이벤트는 플레이어들에게 추가적인 혜택을 제공하고, 카지노 콤프, 페이백 보너스, 미니 게임 이벤트 등도 이용할 수 있습니다.
결제 방식은 다양하게 제공되는데, 플레이어가 가입 시 제공한 정보를 바탕으로 한국 내 은행 송금 서비스를 이용할 수 있습니다. 또한, 핀테크 서비스를 활용한 충전도 가능하여 플레이어는 자신에게 가장 편리한 방법으로 결제를 진행할 수 있습니다.
- 보너스: 첫 충전 시 30%의 웰컴 보너스, 돌발 이벤트로 10~25%의 충전 보너스 제공
- 지원 게임: 라이브카지노, 스포츠 베팅, 바카라, 룰렛, 슬롯 등
- 주요 특징: 국내 은행 결제 가능, 24시간 고객 서비스, 카지노 콤프 보너스 제공
3. 세븐(Seven) – 40%의 신규 고객 회원 보너스 지원의 라이브카지노

세븐 카지노는 몰타 기반의 공식 라이선스를 보유하고 있는 카지노 플랫폼입니다. 라이브 카지노와 슬롯 게임의 경우, 비보 게이밍, 프라그마틱 플레이, 에보플레이와 같은 신뢰할 수 있는 파트너사들로부터 다양한 게임을 제공받고 있습니다.
미니 게임 섹션에서는 파워볼, 바카라, 주사위 게임 등 다양한 게임들을 즐길 수 있으며, 스포츠 분야에서는 국내외의 다양한 리그와 종목을 통해 배팅의 재미를 느낄 수 있습니다. 실시간 배팅 옵션을 통해 경기 도중에도 효율적인 배팅이 가능하고, 배당 계산기와 같은 기능을 활용하여 승률을 높일 수 있습니다.
프로모션과 보너스는 이용자들에게 큰 매력을 제공합니다. 신규 가입자들은 카지노와 스포츠 배팅에 따라 다양한 첫 충전 보너스를 받을 수 있으며, 다양한 플러스 혜택과 프로모션을 통해 더욱 풍성한 게임 경험을 누릴 수 있습니다.
- 보너스: 최대 40%의 첫 충전 보너스, 15% 무제한 충전 보너스와 입금 플러스 혜택, 매주 월요일 5% 페이백 프로모션
- 지원 게임: 라이브 카지노, 스포츠 베팅, 바카라, 룰렛, 잭팟 슬롯, 라이브 딜러 등
- 주요 특징: 10개 게임 제작사 라이브 딜러 게임, 슈퍼볼 등의 미니게임 제공, 뛰어난 스포츠 베팅 셀렉션
4. 엠비트 카지노(mBit Casino) – 광범위한 게임을 제공하는 라이브 딜러 플랫폼
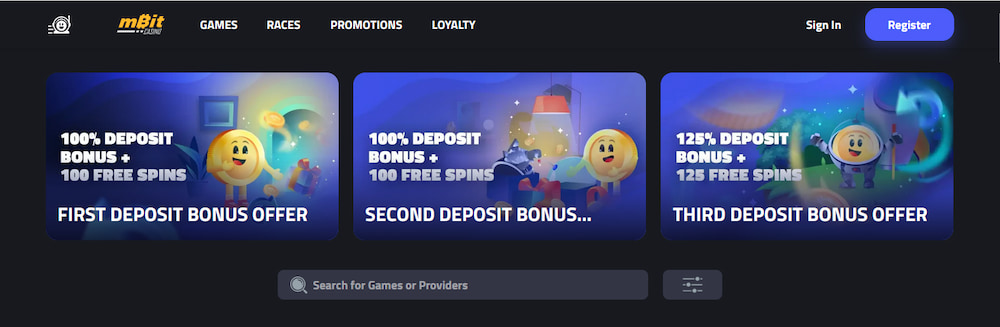
엠비트 카지노는 2014년에 탄생한 퀴라소 기반의 온라인 게임 플랫폼입니다. 이 사이트는 비트코인을 포함한 다양한 암호화폐 보상 방식과 함께 풍부한 게임 콘텐츠를 사용자들에게 제공합니다. 또한, 특별 VIP 프로그램은 다른 경쟁사와 차별화를 둡니다.
이 플랫폼은 모든 디바이스에 맞게 최적화되어 있으며, 최신 게임의 광범위한 컬렉션을 보유하고 있습니다. 사용자 중심의 디자인으로 인해 게임 탐색이 간편하고 빠르게 진행됩니다.
엠비트 카지노에서는 라이브 딜러 게임이 큰 인기를 누리고 있습니다. 특히 에볼루션 게이밍과 같은 업계의 선두주자들과 협력하여 50가지가 넘는 테이블 게임을 제공하고 있습니다. 바카라, 프리미엄 블랙잭, 룰렛 등이 주요 게임 중 일부입니다. 이와 별도로, 플레이어는 자신이 선호하는 라이브 딜러를 선택할 수 있는 기능도 있습니다.
엠비트 카지노는 주로 비트코인을 중심으로 거래되지만 이더리움, 도지코인, 라이트코인과 같은 다른 암호화폐도 지원됩니다. 또한 다양한 모바일 기기로 언제 어디서나 게임을 즐길 수 있으며, 58개 이상의 라이브 딜러 테이블을 통해 여러 게임 플레이가 가능합니다.
- 보너스: 무료 스핀 250회와 110% 예금 매칭 보너스 제공
- 지원 게임: 라이브카지노, 스포츠 베팅, 크래쉬, 블랙잭, 바카라, 잭팟 슬롯 등
- 주요 특징: 다양한 암호화폐 지원, 50개 이상의 여러 라이브 딜러 테이블, 매우 빠른 출금, 에볼루션 게이밍 개발사, 보너스 유효기간 30일
5. 비트슬롯 (BitSlot) – 다양한 슬롯 게임을 제공하는 라이브카지노
비트슬롯은 슬롯 게임에 특화된 온라인 카지노로, 주요 암호화폐 지원이 특징입니다 – 도지코인, 비트코인캐시, 라이트코인, 이더리움, 테더, XRP 등의 다양한 암호화폐로 거래가 가능합니다.
새롭게 가입하는 플레이어들은 처음 4번의 입금에 따른 매력적인 웰컴 보너스를 받을 수 있습니다. 첫 예치 시 최대 1 비트코인까지 100%의 매칭 보너스가 적용되며, 이후 두 번째 예치에는 50% 보너스가 적용됩니다.
이렇게 모든 보너스를 합치면 최대로 5 비트코인을 추가로 얻을 수 있는데, 이에 더해 각 예치 시 무료 스핀이 부여됩니다. 그러나 이 보너스를 현금으로 전환하기 위해서는 35배의 웨이저링 조건을 만족시켜야 하고, 보너스는 7일 동안 유효합니다.
비트슬롯 카지노는 단순히 슬롯만 제공하는 것이 아닙니다. 클래식 카지노 게임과 다양한 비디오 슬롯, 그리고 큰 상금이 걸려있는 잭팟 게임을 포함한 넓은 선택지가 있습니다. 또한, 블랙잭이나 바카라와 같은 라이브 카지노 게임도 즐길 수 있습니다.
- 보너스: 첫 예치 시 100% 매칭 보너스, 두번 째 예치 시 50% 매칭 보너스
- 지원 게임: 라이브카지노, 블랙잭, 바카라, 스포츠 베팅, 비디오 슬롯 등
- 주요 특징: 4차례에 걸친 웰컴 보너스, 다양한 알트코인, 광범위한 게임 제공
6. 비씨게임(BC GAME) – 다양성을 제공하는 최고의 비트코인 라이브 딜러 사이트
이 사이트는 섬세한 그래픽과 다양한 보너스 기회를 자랑합니다. 뿐만 아니라 중앙 관리 없이 작동하는 온라인 도박 플랫폼으로, 모든 게임 활동은 스마트 계약을 통해 투명하게 관리됩니다. 여러 암호화폐도 지원하는 이 플랫폼은 암호화폐에 최적화된 구조로 개발되었습니다.
그 결과 비트코인 등의 암호화폐를 쉽게 입출금할 수 있고, 복잡한 변환 과정 없이 게임에 참여할 수 있습니다. 사용하기 편리한 사용자 인터페이스를 제공하여 사용자들에게 좋은 경험을 제공합니다.
BC.GAME 화면 내에서는 특별한 라이브 게임 섹션을 찾을 수 있습니다. 여기에서는 진짜와 같은 경험을 제공하는 라이브 딜러 게임들이 준비되어 있습니다. 지속적인 업데이트로 게임의 품질을 향상시키고 있습니다.
또한, BC.GAME은 여러 보너스로도 널리 알려져 있습니다. 다양한 아이템을 제공하는 무료 스핀이 주어지며, 이는 일반적인 입금 보너스와 유사합니다. 무료로 받을 수 있는 보상에는 여러 암호화폐가 포함됩니다. 보너스를 받았을 때는 복잡한 요구사항 없이 바로 현금으로 전환할 수 있습니다.
참고! 이 플랫폼은 오로지 암호화폐만을 지원하고, 50여 가지의 암호화폐를 지원하고 있습니다. 그리고 BC GAME만의 특별한 코인인 BCD도 제공되며, 이는 플랫폼 내에서 안정적인 가치를 지닌 코인으로 사용됩니다.
- 보너스: 첫 예치 시 최고 260% 매칭 보너스, 작업 보너스, 마스터 메달 등의 프로모션 제공
- 지원 게임: 라이브카지노, 블랙잭, 룰렛, 라이트닝 룰렛, 바카라 등
- 주요 특징: 100개 이상의 라이브 딜러 게임, KYC 요구 없음, 에볼루션 게임을 비롯한 유명 카지노 게임 개발사
라이브 카지노 실전 전략 가이드: 플레이어가 알아야 할 핵심 전략
라이브 카지노는 한국 뿐만 아니라 전세계적으로 수많은 게임 애호가들에게 큰 인기를 끌고 있습니다. 게임의 현실감 넘치는 경험과 경제적인 수익이 결합되어 이러한 주목을 받고 있습니다. 그러나 라이브 카지노에서 성공하려면 단순한 운만으로는 충분하지 않습니다. 신중한 판단과 전략적인 접근이 필수적입니다. 아래, 온라인 라이브 카지노에서 성공을 위한 몇 가지 중요한 전략들을 소개합니다:
✅ 1. 게임 규칙의 완벽한 이해: 모든 카지노 게임마다 별도의 규칙과 전략이 존재합니다. 예를 들어, 블랙잭이나 포커에서는 기본 전략과 확률을 정확히 알고 있어야 합니다. 장기적으로 승률을 높이려면 이러한 정보를 정확히 이해해야 합니다.
✅ 2. 특정 게임에 전문화: 한 두 가지의 게임에 집중하고 해당 게임의 전략과 세부 사항을 깊게 파악하십시오. 예를 들면, 룰렛에서는 베팅 전략과 확률 분포를 잘 이해하는 것이 중요할 수 있습니다.
✅ 3. 자본 관리 전략 활용: 베팅 규모를 조절하거나 일정한 규칙을 설정하여 자본을 효과적으로 관리하십시오. 이렇게 함으로써 장기적인 손실 위험을 줄일 수 있습니다.
✅ 4. 최신 기술 도구 활용: 많은 라이브 카지노 플랫폼들은 플레이어의 게임 습관과 전략을 도와주는 다양한 도구를 제공합니다. 최근 게임 결과나 승률, 플레이어별 게임 성과 등의 통계 데이터들을 활용하여 자신의 전략을 지속적으로 수정하고 개선하십시오.
✅ 5. 실시간 게임 관찰: 라이브 카지노 게임 중에는 실시간으로 다른 플레이어의 전략과 게임 스타일을 관찰할 수 있는 기회가 많습니다. 이를 통해 자신의 전략을 조절하고 다양한 상황에서의 대응 능력을 향상시킬 수 있습니다.
최고의 라이브카지노 사이트를 찾는 방법
최고의 라이브 카지노를 선택하는 것은 매우 중요한 결정입니다. 온라인 상에는 다양한 라이브 카지노가 존재하지만 안전하고 뛰어난 게임 경험을 위해서는 몇 가지 주요 요소를 고려해야 합니다.
첫째, 라이브 카지노의 신뢰성과 라이선스를 확인하세요. 국제적으로 인정받는 라이선스를 보유한 사이트는 게임의 공정성과 안전성을 보장합니다. 이러한 조건이 갖춰지면 사용자들은 게임을 더욱 안심하고 즐길 수 있습니다.
둘째, 다양한 게임 옵션을 제공하는지 살펴보세요. 다양한 테이블 게임과 카드 게임을 제공하는 사이트는 사용자에게 다양한 선택의 기회를 제공하며, 더욱 풍부한 게임 경험을 선사합니다.
셋째, 안전한 결제 방법은 필수적입니다. 결제 시스템이 신뢰할 수 있고 보안이 철저하게 되어 있다면, 사용자들은 금전적인 거래를 안전하게 진행할 수 있습니다. SSL 암호화나 다양한 결제 방식을 지원하는 사이트는 더욱 안전하게 게임을 즐길 수 있습니다.
마지막으로, 사이트 내 고객 서비스의 중요성을 간과하지 마세요. 24시간 지원과 다양한 연락 방법을 제공하는 라이브 카지노는 사용자의 문제나 질문에 신속하게 응답하여 더욱 안전한 게임 환경을 제공합니다.
라이브 카지노의 보안과 공정한 게임 환경
라이브 카지노의 보안과 공정한 게임 환경은 사용자들에게 중요한 요소로 여겨집니다. 안전하고 공정한 게임 환경을 제공하는 사이트는 사용자에게 더욱 큰 만족감을 주게 됩니다. 그렇다면 라이브 카지노는 어떻게 이러한 보안과 공정성을 보장하는지 살펴보겠습니다:
- 암호화 기술: 고급 암호화 기술을 활용하여 플레이어의 개인 정보와 금전 거래를 안전하게 보호합니다.
- 개인 정보 보호: 플레이어의 개인 정보는 철저한 관리와 안전한 저장을 통해 외부의 무단 액세스로부터 보호됩니다.
- 실시간 게임 방송: 실시간으로 방송되는 게임은 모든 플레이어에게 동일한 게임 환경을 제공하여 공정한 경쟁 환경을 보장합니다.
- 독립적인 검증 기관: 많은 온라인 라이브 카지노들은 독립적인 검증 기관에 의해 게임 결과와 보안 절차의 정확성을 확인 받고 있어 플레이어들에게 게임의 신뢰성과 정직성을 입증합니다.
마치며
온라인 카지노는 화려한 그래픽, 실시간 게임 플레이, 그리고 고급 분석 기능으로 한국 게임 애호가들 사이에서 큰 인기를 끌고 있습니다. 본문에서는 한국의 전문 카지노 딜러가 주도하는 게임 플랫폼을 포함하여 7가지 베스트 온라인 카지노 사이트들을 소개하였습니다. 이러한 플랫폼들은 안전한 결제 시스템, 신속한 입출금 절차, 그리고 사용자 친화적인 인터페이스를 중시하여 제작되었습니다.
다양한 카지노 플랫폼들은 각각 특별한 특징과 장점을 가지고 있어 한국 플레이어들에게 여러 선택의 기회와 스릴 넘치는 경험을 제공합니다. 특히, 실시간 게임 옵션과 고급 분석 기능으로 사용자들은 전략적인 게임 플레이가 가능합니다. 이제 라이브카지노의 스릴 넘치는 체험을 하실 준비가 되셨나요? 지금 바로, 추천 드린 온라인 카지노 사이트를 방문하셔서 다양한 게임을 즐기시고 승리를 거머쥐세요!

자주 묻는 질문
Q1: 라이브 카지노와 일반 온라인 카지노의 차이점은 무엇인가요?
A1: 라이브 카지노는 실시간으로 딜러와 상호 작용하면서 게임을 즐길 수 있는 카지노를 말합니다. 웹캠으로 실제 딜러가 카드를 나누거나 룰렛을 돌리는 모습을 볼 수 있습니다. 반면 일반 온라인 카지노는 컴퓨터 프로그램을 기반으로 동작하며 실시간 상호작용이 없습니다.
Q2: 라이브 카지노에서는 어떤 게임을 즐길 수 있나요?
A2: 라이브 카지노에서는 블랙잭, 룰렛, 바카라, 포커 등 다양한 테이블 게임을 실시간으로 즐길 수 있습니다. 제공되는 게임은 카지노 사이트마다 다를 수 있으니, 특정 카지노의 게임 목록을 확인해보세요.
Q3: 라이브 카지노에서의 연결이 끊어질 경우 어떻게 되나요?
A3: 대부분의 라이브 카지노는 연결이 끊길 경우 게임이 일시 중단됩니다. 연결이 다시 복구되면 게임을 계속 진행할 수 있습니다. 만약 연결이 복구되지 않는 경우, 대부분의 카지노는 투자한 돈을 반환해주거나 해당 게임을 다시 시작할 수 있게 도와줍니다.